6.1 System Hacking Concepts
6.2 Common OS Exploits
6.3 Buffer Overflows
6.3.1 Activity - Performing a Buffer Overflow
6.4 System Hacking Tools and Frameworks
6.4.1 Activity - Hack a Linux Target from Start to Finish
6.5 Metasploit
6.5.1 Activity - Get Started with Metasploit
6.6 Meterpreter
6.7 Keylogging and Spyware
6.7.1 Activity - Keylogging with Meterpreter
6.8 Netcat
6.8.1 Activity - Using Netcat
6.9 Hacking Windows
6.9.1 Activity - Hacking Windows with Eternal Blue
6.10 Hacking Linux
6.11 Password Attacks
6.11.1 Activity - Pass the Hash
6.11.2 Activity - Password Spraying
6.12 Password Cracking Tools
6.13 Windows Password Cracking
6.13.1 Activity - Cracking Windows Passwords
6.13.2 Activity - Cracking Password Hashes with Hashcat
6.14 Linux Password Cracking
6.15 Other Methods for Obtaining Passwords
6.16 Network Service Attacks
6.16.1 Activity - Brute Forcing a Network Service with Medusa
6.17 Post Exploitation
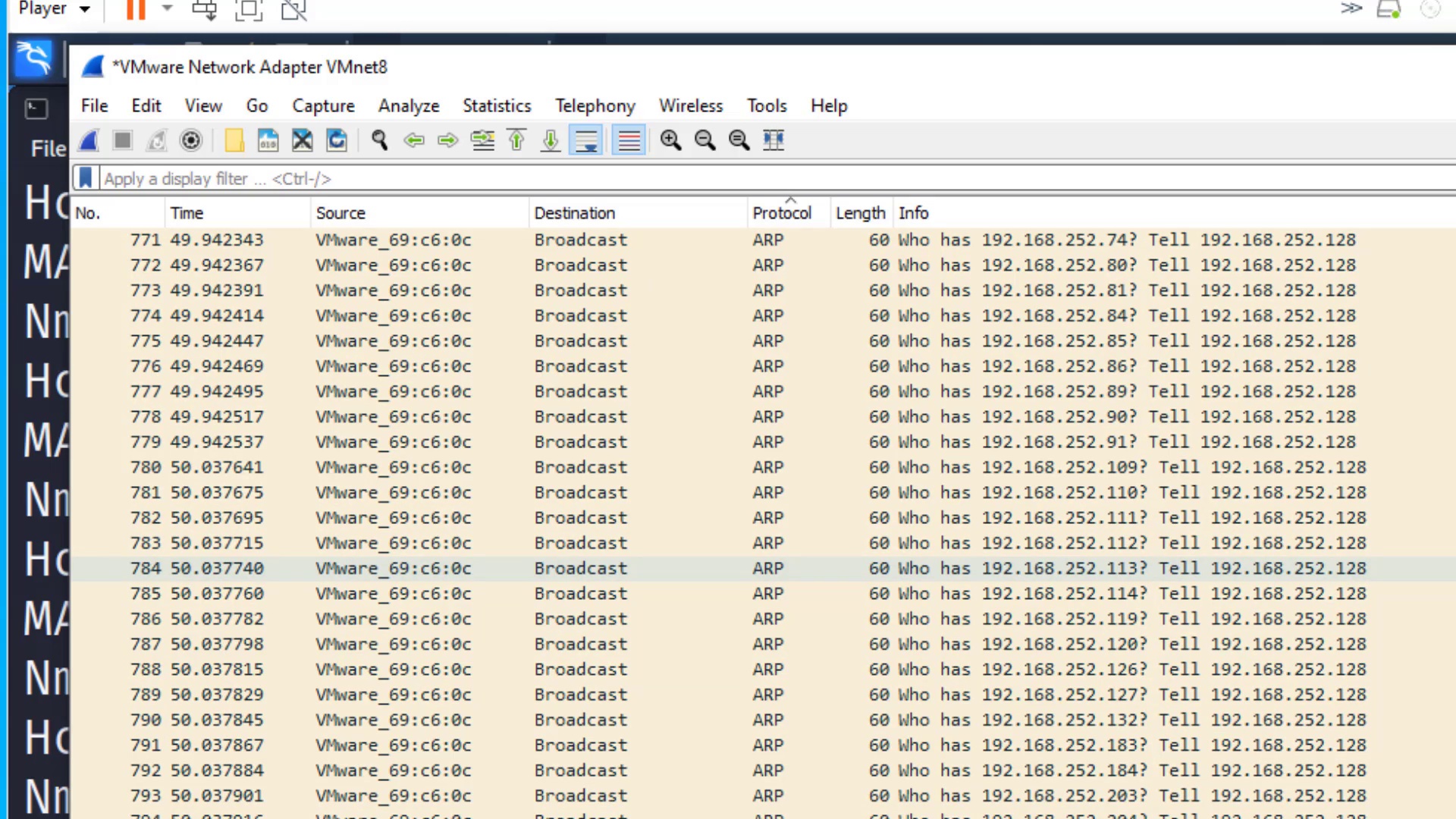
6.18 Pivoting
6.18.1 Activity - Pivoting Setup
6.19 Maintaining Access
6.19.1 Activity - Persistence
6.20 Hiding Data
6.20.1 Activity - Hiding Data Using Least Significant Bit Steganography
6.21 Covering Tracks
6.21.1 Activity - Clearing Tracks in Windows
6.21.2 Activity - View and Clear Audit Policies with Auditpol
6.22 System Hacking Countermeasures
6.23 System Hacking Review