001 - CompTIA Cybersecurity Analyst (CySA+) CS0-002 Introduction - CompTIA Cybersecurity Analyst (CySA+) CS0-002
002 - Module introduction - CompTIA Cybersecurity Analyst (CySA+) CS0-002
003 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
004 - 1.1 What is Threat Intelligence - CompTIA Cybersecurity Analyst (CySA+) CS0-002
005 - 1.2 Threat Sources - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
006 - 1.3 Threat Sources - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
007 - 1.4 Threat Classifications - CompTIA Cybersecurity Analyst (CySA+) CS0-002
008 - 1.5 Cyber Threat Investigation - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
009 - 1.6 Cyber Threat Investigation - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
010 - 1.7 Social Media Graphs - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
011 - 1.8 Social Media Graphs - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
012 - 1.9 Log Challenges - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
013 - 1.10 Log Challenges - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
014 - 1.11 Advanced Threat Hunting - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
015 - 1.12 Advanced Threat Hunting - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
016 - 1.13 Endpoint Detection - CompTIA Cybersecurity Analyst (CySA+) CS0-002
017 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
018 - 2.1 Attack Frameworks - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
019 - 2.2 Attack Frameworks - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
020 - 2.3 Threat Research - CompTIA Cybersecurity Analyst (CySA+) CS0-002
021 - 2.4 Threat Modeling Methodologies and Threat Intelligence Sharing with Support Functions - CompTIA Cybersecurity Analyst (CySA+) CS0-002
022 - 2.5 Wireless Analysis Techniques - CompTIA Cybersecurity Analyst (CySA+) CS0-002
023 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
024 - 3.1 Vulnerability Identification - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
025 - 3.2 Vulnerability Identification - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
026 - 3.3 Validation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
027 - 3.4 Remediation and Mitigation and Inhibitors - CompTIA Cybersecurity Analyst (CySA+) CS0-002
028 - 3.5 Scanning Parameters and Criteria - CompTIA Cybersecurity Analyst (CySA+) CS0-002
029 - 3.6 Vulnerability Scanning - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
030 - 3.7 Vulnerability Scanning - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
031 - 3.8 Enumeration - CompTIA Cybersecurity Analyst (CySA+) CS0-002
032 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
033 - 4.1 Understanding Results - CompTIA Cybersecurity Analyst (CySA+) CS0-002
034 - 4.2 Web Application Scanners - CompTIA Cybersecurity Analyst (CySA+) CS0-002
035 - 4.3 Infrastructure Vulnerability Scanner - CompTIA Cybersecurity Analyst (CySA+) CS0-002
036 - 4.4 Software Assessment Tools and Techniques - CompTIA Cybersecurity Analyst (CySA+) CS0-002
037 - 4.5 Wireless Assessment - CompTIA Cybersecurity Analyst (CySA+) CS0-002
038 - 4.6 Cloud Infrastructure Assessment - CompTIA Cybersecurity Analyst (CySA+) CS0-002
039 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
040 - 5.1 Mobile - CompTIA Cybersecurity Analyst (CySA+) CS0-002
041 - 5.2 Internet of Things (IoT) and Embedded Devices - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
042 - 5.3 Internet of Things (IoT) and Embedded Devices - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
043 - 5.4 APTs - CompTIA Cybersecurity Analyst (CySA+) CS0-002
044 - 5.5 Embedded and Real-Time Operating Systems (RTOS) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
045 - 5.6 SOC and FPGA - CompTIA Cybersecurity Analyst (CySA+) CS0-002
046 - 5.7 Physical Access Control - CompTIA Cybersecurity Analyst (CySA+) CS0-002
047 - 5.8 Building Automation Systems, Vehicles, and Drones - CompTIA Cybersecurity Analyst (CySA+) CS0-002
048 - 5.9 Industrial Control Systems (ICS) and Process Automation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
049 - 5.10 Defending Critical Infrastructure - CompTIA Cybersecurity Analyst (CySA+) CS0-002
050 - 5.11 Supervisory Control and Data Acquisition (SCADA) - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
051 - 5.12 Supervisory Control and Data Acquisition (SCADA) - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
052 - 5.13 Verifications and Quality Controls - CompTIA Cybersecurity Analyst (CySA+) CS0-002
053 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
054 - 6.1 Cloud Service, FaaS, and Deployment Models - CompTIA Cybersecurity Analyst (CySA+) CS0-002
055 - 6.2 IaC, Insecure Applications - CompTIA Cybersecurity Analyst (CySA+) CS0-002
056 - 6.3 Application Programming Interface - CompTIA Cybersecurity Analyst (CySA+) CS0-002
057 - 6.4 Improper Key Management - CompTIA Cybersecurity Analyst (CySA+) CS0-002
058 - 6.5 Logging and Monitoring - CompTIA Cybersecurity Analyst (CySA+) CS0-002
059 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
060 - 7.1 Attack Types and XML Types - CompTIA Cybersecurity Analyst (CySA+) CS0-002
061 - 7.2 SQL Attacks - CompTIA Cybersecurity Analyst (CySA+) CS0-002
062 - 7.3 Overflow Attacks - CompTIA Cybersecurity Analyst (CySA+) CS0-002
063 - 7.4 Cross-Site Scripting - CompTIA Cybersecurity Analyst (CySA+) CS0-002
064 - 7.5 Remote Code Execution - CompTIA Cybersecurity Analyst (CySA+) CS0-002
065 - 7.6 Directory Traversal - CompTIA Cybersecurity Analyst (CySA+) CS0-002
066 - 7.7 Privilege Escalation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
067 - 7.8 Password Spraying - CompTIA Cybersecurity Analyst (CySA+) CS0-002
068 - 7.9 Credential Stuffing - CompTIA Cybersecurity Analyst (CySA+) CS0-002
069 - 7.10 Impersonation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
070 - 7.11 On-path and Man-in-the-Middle - CompTIA Cybersecurity Analyst (CySA+) CS0-002
071 - 7.12 Session Hijacking - CompTIA Cybersecurity Analyst (CySA+) CS0-002
072 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
073 - 8.1 Vulnerabilities & Improper Error Handling - CompTIA Cybersecurity Analyst (CySA+) CS0-002
074 - 8.2 Dereferencing - CompTIA Cybersecurity Analyst (CySA+) CS0-002
075 - 8.3 Insecure Object Reference - CompTIA Cybersecurity Analyst (CySA+) CS0-002
076 - 8.4 Race Condition - CompTIA Cybersecurity Analyst (CySA+) CS0-002
077 - 8.5 Broker Authentication - CompTIA Cybersecurity Analyst (CySA+) CS0-002
078 - 8.6 Sensitive Data Exposure - CompTIA Cybersecurity Analyst (CySA+) CS0-002
079 - 8.7 Insecure Components - CompTIA Cybersecurity Analyst (CySA+) CS0-002
080 - 8.8 Insufficient Logging and Monitoring - CompTIA Cybersecurity Analyst (CySA+) CS0-002
081 - 8.9 Weak or Default Configurations - CompTIA Cybersecurity Analyst (CySA+) CS0-002
082 - Module introduction - CompTIA Cybersecurity Analyst (CySA+) CS0-002
083 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
084 - 9.1 Cloud vs. On-premises - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
085 - 9.2 Cloud vs. On-premises - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
086 - 9.3 Asset Management - CompTIA Cybersecurity Analyst (CySA+) CS0-002
087 - 9.4 Segmentation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
088 - 9.5 Network Architecture - CompTIA Cybersecurity Analyst (CySA+) CS0-002
089 - 9.6 Change Management - CompTIA Cybersecurity Analyst (CySA+) CS0-002
090 - 9.7 Containerization - CompTIA Cybersecurity Analyst (CySA+) CS0-002
091 - 9.8 Identity and Access Management - CompTIA Cybersecurity Analyst (CySA+) CS0-002
092 - 9.9 Cloud Access Security Broker (CASB) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
093 - 9.10 Honeypots and Breach Detection - CompTIA Cybersecurity Analyst (CySA+) CS0-002
094 - 9.11 Encryption and Certificate Management - CompTIA Cybersecurity Analyst (CySA+) CS0-002
095 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
096 - 10.1 SDLC Platforms - CompTIA Cybersecurity Analyst (CySA+) CS0-002
097 - 10.2 DevSecOps - CompTIA Cybersecurity Analyst (CySA+) CS0-002
098 - 10.3 Software Assessment Methods - CompTIA Cybersecurity Analyst (CySA+) CS0-002
099 - 10.4 User Acceptance Training and Stress Test - CompTIA Cybersecurity Analyst (CySA+) CS0-002
100 - 10.5 Security Regression Training - CompTIA Cybersecurity Analyst (CySA+) CS0-002
101 - 10.6 Code Review - CompTIA Cybersecurity Analyst (CySA+) CS0-002
102 - 10.7 Secure Coding Best Practices - CompTIA Cybersecurity Analyst (CySA+) CS0-002
103 - 10.8 Input Validation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
104 - 10.9 Output Encoding - CompTIA Cybersecurity Analyst (CySA+) CS0-002
105 - 10.10 Session Management - CompTIA Cybersecurity Analyst (CySA+) CS0-002
106 - 10.11 Authentication - CompTIA Cybersecurity Analyst (CySA+) CS0-002
107 - 10.12 Data Protection - CompTIA Cybersecurity Analyst (CySA+) CS0-002
108 - 10.13 Paramaterized Queries - CompTIA Cybersecurity Analyst (CySA+) CS0-002
109 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
110 - 11.1 Hardware Root of Trust - CompTIA Cybersecurity Analyst (CySA+) CS0-002
111 - 11.2 Trusted Platform Module (TPM) and Hardware Security Module (HSM) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
112 - 11.3 Unified Extensible Firmware Interface (UEFI) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
113 - Module introduction - CompTIA Cybersecurity Analyst (CySA+) CS0-002
114 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
115 - 12.1 Event Logs - CompTIA Cybersecurity Analyst (CySA+) CS0-002
116 - 12.2 Syslogs - CompTIA Cybersecurity Analyst (CySA+) CS0-002
117 - 12.3 Firewall Logs - CompTIA Cybersecurity Analyst (CySA+) CS0-002
118 - 12.4 Web Application Firewall (WAF) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
119 - 12.5 Proxy - CompTIA Cybersecurity Analyst (CySA+) CS0-002
120 - 12.6 Intrusion Detection and Prevention (IDS IPS) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
121 - 12.7 Impact Analysis - CompTIA Cybersecurity Analyst (CySA+) CS0-002
122 - 12.8 Organizations Impact vs. Localized Impact - CompTIA Cybersecurity Analyst (CySA+) CS0-002
123 - 12.9 Immediate vs. Total - CompTIA Cybersecurity Analyst (CySA+) CS0-002
124 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
125 - 13.1 Security Information and Event Management (SIEM) - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
126 - 13.2 Security Information and Event Management (SIEM) - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
127 - 13.3 Rule Writing - CompTIA Cybersecurity Analyst (CySA+) CS0-002
128 - 13.4 Known-bad Internet Protocol (IP) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
129 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
130 - 14.1 Malicious Payload - CompTIA Cybersecurity Analyst (CySA+) CS0-002
131 - 14.2 Domain Keys Identified Mail (DKIM) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
132 - 14.3 Domain-based Message - CompTIA Cybersecurity Analyst (CySA+) CS0-002
133 - 14.4 Embedded Links - CompTIA Cybersecurity Analyst (CySA+) CS0-002
134 - 14.5 Impersonation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
135 - 14.6 Header - CompTIA Cybersecurity Analyst (CySA+) CS0-002
136 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
137 - 15.1 Change Control - CompTIA Cybersecurity Analyst (CySA+) CS0-002
138 - 15.2 Allow List - CompTIA Cybersecurity Analyst (CySA+) CS0-002
139 - 15.3 Blocklist - CompTIA Cybersecurity Analyst (CySA+) CS0-002
140 - 15.4 Firewall - CompTIA Cybersecurity Analyst (CySA+) CS0-002
141 - 15.5 Intrusion Prevention System (IPS) Rules - CompTIA Cybersecurity Analyst (CySA+) CS0-002
142 - 15.6 Data Loss Prevention (DLP) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
143 - 15.7 Endpoint Detection and Response (EDR) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
144 - 15.8 Network Access Control (NAC) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
145 - 15.9 Sinkholing - CompTIA Cybersecurity Analyst (CySA+) CS0-002
146 - 15.10 Malware Signature Rule Writing - CompTIA Cybersecurity Analyst (CySA+) CS0-002
147 - 15.11 Sandboxing - CompTIA Cybersecurity Analyst (CySA+) CS0-002
148 - 15.12 Port Security - CompTIA Cybersecurity Analyst (CySA+) CS0-002
149 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
150 - 16.1 Establishing a Hypothesis - CompTIA Cybersecurity Analyst (CySA+) CS0-002
151 - 16.2 Profiling Threat Actors and Activities - CompTIA Cybersecurity Analyst (CySA+) CS0-002
152 - 16.3 Reducing the Attack Surface Area - CompTIA Cybersecurity Analyst (CySA+) CS0-002
153 - 16.4 Bundling Critical Assets - CompTIA Cybersecurity Analyst (CySA+) CS0-002
154 - 16.5 Attack Vectors - CompTIA Cybersecurity Analyst (CySA+) CS0-002
155 - 16.6 Integrated Intelligence - CompTIA Cybersecurity Analyst (CySA+) CS0-002
156 - 16.7 Improving Detection Capabilities - CompTIA Cybersecurity Analyst (CySA+) CS0-002
157 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
158 - 17.1 Workflow Orchestration - CompTIA Cybersecurity Analyst (CySA+) CS0-002
159 - 17.2 Security Orchestration - CompTIA Cybersecurity Analyst (CySA+) CS0-002
160 - 17.3 Security Orchestration, Automation, and Response (SOAR) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
161 - 17.4 Scripting - CompTIA Cybersecurity Analyst (CySA+) CS0-002
162 - 17.5 Application Programming Interface (API) Integration - CompTIA Cybersecurity Analyst (CySA+) CS0-002
163 - 17.6 Automated Malware Signature Creation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
164 - 17.7 Data Encrichment - CompTIA Cybersecurity Analyst (CySA+) CS0-002
165 - 17.8 Threat Feed Combination - CompTIA Cybersecurity Analyst (CySA+) CS0-002
166 - 17.9 Machine Learning - CompTIA Cybersecurity Analyst (CySA+) CS0-002
167 - 17.10 Security Content Automation Protocol (SCAP) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
168 - 17.11 Continuous Integration - CompTIA Cybersecurity Analyst (CySA+) CS0-002
169 - 17.12 Continuous Deployment and Delivery - CompTIA Cybersecurity Analyst (CySA+) CS0-002
170 - Module introduction - CompTIA Cybersecurity Analyst (CySA+) CS0-002
171 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
172 - 18.1 What is a Cyber Incident - CompTIA Cybersecurity Analyst (CySA+) CS0-002
173 - 18.2 Communication Plan - CompTIA Cybersecurity Analyst (CySA+) CS0-002
174 - 18.3 Trusted Parties - CompTIA Cybersecurity Analyst (CySA+) CS0-002
175 - 18.4 Regulatory and Legislative Requirements - CompTIA Cybersecurity Analyst (CySA+) CS0-002
176 - 18.5 Preventing Inadvertent Release of Information - CompTIA Cybersecurity Analyst (CySA+) CS0-002
177 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
178 - 19.1 Legal - CompTIA Cybersecurity Analyst (CySA+) CS0-002
179 - 19.2 Human Resources - CompTIA Cybersecurity Analyst (CySA+) CS0-002
180 - 19.3 Public Relations - CompTIA Cybersecurity Analyst (CySA+) CS0-002
181 - 19.4 Senior Leadership - CompTIA Cybersecurity Analyst (CySA+) CS0-002
182 - 19.5 Regulatory Bodies - CompTIA Cybersecurity Analyst (CySA+) CS0-002
183 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
184 - 20.1 Personal Identifiable Information (PII) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
185 - 20.2 Personal Health Information (PHI) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
186 - 20.3 Sensitive Personal Information (SPI) and High Value Assets - CompTIA Cybersecurity Analyst (CySA+) CS0-002
187 - 20.4 Intellectual Property - CompTIA Cybersecurity Analyst (CySA+) CS0-002
188 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
189 - 21.1 Preparation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
190 - 21.2 Training - CompTIA Cybersecurity Analyst (CySA+) CS0-002
191 - 21.3 Testing - CompTIA Cybersecurity Analyst (CySA+) CS0-002
192 - 21.4 Document Procedures - CompTIA Cybersecurity Analyst (CySA+) CS0-002
193 - 21.5 Detection and Analysis - CompTIA Cybersecurity Analyst (CySA+) CS0-002
194 - 21.6 Severity Level Classification - CompTIA Cybersecurity Analyst (CySA+) CS0-002
195 - 21.7 Downtime - CompTIA Cybersecurity Analyst (CySA+) CS0-002
196 - 21.8 Recovery Time - CompTIA Cybersecurity Analyst (CySA+) CS0-002
197 - 21.9 Reverse Engineering - CompTIA Cybersecurity Analyst (CySA+) CS0-002
198 - 21.10 Containment and Isolation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
199 - Module introduction - CompTIA Cybersecurity Analyst (CySA+) CS0-002
200 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
201 - 22.1 Privacy vs. Security - CompTIA Cybersecurity Analyst (CySA+) CS0-002
202 - 22.2 Non-technical Controls - CompTIA Cybersecurity Analyst (CySA+) CS0-002
203 - 22.3 Classification, Ownership, Retention, and Data Types - CompTIA Cybersecurity Analyst (CySA+) CS0-002
204 - 22.4 Confidentiality, Legal Requirements, and Data Sovereignty - CompTIA Cybersecurity Analyst (CySA+) CS0-002
205 - 22.5 Data Minimization, Purpose Limitation, and NDA - CompTIA Cybersecurity Analyst (CySA+) CS0-002
206 - 22.6 Technical Controls - CompTIA Cybersecurity Analyst (CySA+) CS0-002
207 - 22.7 Encryption - CompTIA Cybersecurity Analyst (CySA+) CS0-002
208 - 22.8 Data Loss Prevention (DLP) - CompTIA Cybersecurity Analyst (CySA+) CS0-002
209 - 22.9 Data Masking and Deidentification - CompTIA Cybersecurity Analyst (CySA+) CS0-002
210 - 22.10 Tokenization - CompTIA Cybersecurity Analyst (CySA+) CS0-002
211 - 22.11 Digital Rights Management (DRM) and Watermarking - CompTIA Cybersecurity Analyst (CySA+) CS0-002
212 - 22.12 Geographic Access Requirements - CompTIA Cybersecurity Analyst (CySA+) CS0-002
213 - 22.13 Access Controls - CompTIA Cybersecurity Analyst (CySA+) CS0-002
214 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
215 - 23.1 Business Impact and Risk Calculation - CompTIA Cybersecurity Analyst (CySA+) CS0-002
216 - 23.2 Communication Risk Factors and Risk Prioritization - CompTIA Cybersecurity Analyst (CySA+) CS0-002
217 - 23.3 System Assessments - CompTIA Cybersecurity Analyst (CySA+) CS0-002
218 - 23.4 Compensating Controls and Training - Part 1 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
219 - 23.5 Compensating Controls and Training - Part 2 - CompTIA Cybersecurity Analyst (CySA+) CS0-002
220 - 23.6 Supply Chain Assessment - CompTIA Cybersecurity Analyst (CySA+) CS0-002
221 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
222 - 24.1 Frameworks - CompTIA Cybersecurity Analyst (CySA+) CS0-002
223 - 24.2 AUP, Password Policies, Data Ownership, and Other Procedures - CompTIA Cybersecurity Analyst (CySA+) CS0-002
224 - 24.3 Control Types - CompTIA Cybersecurity Analyst (CySA+) CS0-002
225 - 24.4 Audits and Assessments - CompTIA Cybersecurity Analyst (CySA+) CS0-002
226 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
227 - 25.1 Malware Threat Landscape - CompTIA Cybersecurity Analyst (CySA+) CS0-002
228 - 25.2 Malware Analysis - CompTIA Cybersecurity Analyst (CySA+) CS0-002
229 - 25.3 Malware Analysis Overview - CompTIA Cybersecurity Analyst (CySA+) CS0-002
230 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
231 - 26.1 Why Set Up a Malware Lab - CompTIA Cybersecurity Analyst (CySA+) CS0-002
232 - 26.2 How to Correctly Set Up a Lab - CompTIA Cybersecurity Analyst (CySA+) CS0-002
233 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
234 - 27.1 Cuckoo Sandbox - CompTIA Cybersecurity Analyst (CySA+) CS0-002
235 - 27.2 Other Sandbox Systems - CompTIA Cybersecurity Analyst (CySA+) CS0-002
236 - 27.3 Networking and Internet Connections - CompTIA Cybersecurity Analyst (CySA+) CS0-002
237 - 27.4 Sandbox and Network - CompTIA Cybersecurity Analyst (CySA+) CS0-002
238 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
239 - 28.1 Wireshark - CompTIA Cybersecurity Analyst (CySA+) CS0-002
240 - 28.2 Column Setup - CompTIA Cybersecurity Analyst (CySA+) CS0-002
241 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
242 - 29.1 PE File Format - CompTIA Cybersecurity Analyst (CySA+) CS0-002
243 - 29.2 Image Header - CompTIA Cybersecurity Analyst (CySA+) CS0-002
244 - 29.3 Entry Points - CompTIA Cybersecurity Analyst (CySA+) CS0-002
245 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
246 - 30.1 Registry Persistence - CompTIA Cybersecurity Analyst (CySA+) CS0-002
247 - 30.2 Analyzing for Persistence - CompTIA Cybersecurity Analyst (CySA+) CS0-002
248 - 30.3 Other Techniques - CompTIA Cybersecurity Analyst (CySA+) CS0-002
249 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
250 - 31.1 What to Look for - CompTIA Cybersecurity Analyst (CySA+) CS0-002
251 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
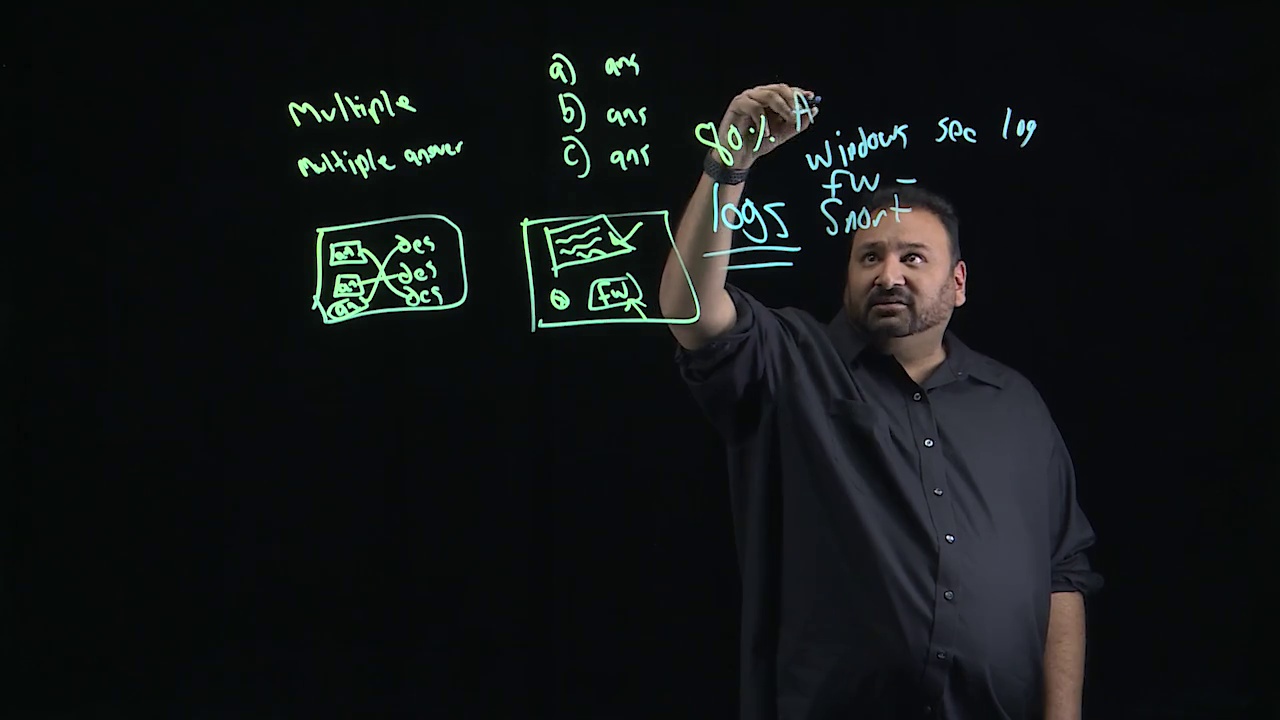
252 - 32.1 Understanding the Test - CompTIA Cybersecurity Analyst (CySA+) CS0-002
253 - 32.2 Type of Test Questions - CompTIA Cybersecurity Analyst (CySA+) CS0-002
254 - 32.3 Increasing Your Chances for Passing the Test - CompTIA Cybersecurity Analyst (CySA+) CS0-002
255 - 32.4 Certification Review - CompTIA Cybersecurity Analyst (CySA+) CS0-002
256 - Learning objectives - CompTIA Cybersecurity Analyst (CySA+) CS0-002
257 - 33.1 What I Learned - CompTIA Cybersecurity Analyst (CySA+) CS0-002
258 - CompTIA Cybersecurity Analyst (CySA+) CS0-002 Summary - CompTIA Cybersecurity Analyst (CySA+) CS0-002